【alyce mahon introduction to eroticism and art 2007】
Editor's note: We have alyce mahon introduction to eroticism and art 2007published an updated guide to the Dark Web here.
You may have heard about this mysterious place on the Internet called the 'Deep Web'. Interest in the deep web and dark web arose following a few high profile data leaks, a growing interest in online privacy, references in mainstream media, and the widely publicized FBI investigation into online marketplace Silk Road that exposed the extent of online drug trafficking.
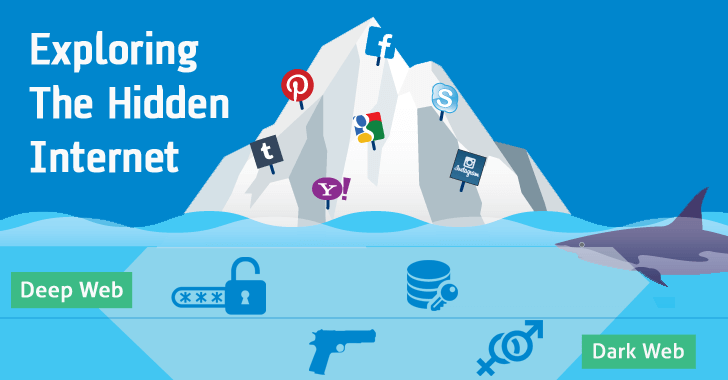
But what is exactly the deep web? Well it's not actually a 'place' but rather anywhere other than the visible web that is crawled, indexed and accessed through links fetched by search engines like Google. The deep web is actually several times bigger than the indexed web, and it encompasses a lot more than the illegal or otherwise questionable activities that it is often associated with – though there's certainly a lot of that going on, too. Let's start by clearing up some of the confusion among the different terms that tend to be thrown around while discussing the Internet's underground.
Surface Web, Deep Web, Dark Web
In simple terms, the Surface Web is anything that a search engine can find by crawling links and identifying content online, while the Deep Web is anything that a search engine can't find. The Dark Web on the other hand merely represents a smaller portion of the deep web that has been intentionally hidden and is inaccessible through standard web browsers.
To exemplify this a bit further, the deep web can actually include things like academic databases, which can be accessed through a normal browser but are not accessible to search engines.
It also includes content within mainstream websites that is simply not set up to be accessed through a search engine. For example content posted on Facebook that is only available to the poster's friends, not the general public, or results for specific queries on a travel booking website – you simply can't get to the content by clicking through links like a search engine would.
Accessing the Dark Web
The Tor network is the most commonly known place where dark web content resides. This anonymous network consists of thousands of servers located all over the world run by volunteers and online privacy advocates. Its name is an acronym for 'The Onion Router' in reference to its namesake routing technique, which creates a path through randomly assigned Tor servers, or nodes, before reaching whatever website you are visiting. During this process data packets are wrapped in successive layers of packets that get "peeled off" at each node until reaching the destination.
Here is a more technical explanation, but in concise terms, the result is that no one node knows the complete path between your computer and a website, only the last place the packet was, and the next place it will be. This makes it almost impossible for anyone to trace the traffic back to you.
While finding content on the dark web can take time and plenty of patience, technically, accessing the Tor network isn't that complicated at all. You simply need to download and install the Tor browser available for Windows, macOS, and Linux. It is no different from installing any other piece of software and it's very simple to use as it's just a modified version of Firefox.
Protecting Yourself
If you're serious about the security of whatever it is you're doing on the dark web, it's worth running an entirely separate environment from your main computer and internet connection. Tails OS is a bootable operating system that's already preconfigured to maximize privacy and that you can run from a USB stick or a virtual machine. Tails has an installation wizard that guides you step-by-step through the process of setting up the software so that shouldn't pose much of a challenge either. Tails received a lot of press when it was disclosed that Edward Snowden was using it to avoid NSA snooping. Its sole purpose is preserving your privacy and anonymity online by relying on the Tor network and other tools to keep your activity secret.
Layering your location by starting at a random Wi-Fi hotspot and then connecting to a VPN before loading Tor will greatly increase your odds of anonymity.
We have written a more thorough, dedicated article to keeping yourself safe while surfing the seedy underbelly of the web. You can read that here.
Search
Categories
Latest Posts
Yes, that was Ke Huy Quan on the phone in 'The White Lotus' Season 3
2025-06-26 23:04Hundreds of frozen pizzas left on highway after truck crashes
2025-06-26 22:03The Ultimate Guide to Protecting Your Identity in the Digital Age
2025-06-26 21:51Popular Posts
FaceApp removes racist 'ethnicity change' face filters from its app
2025-06-26 22:39Uber is rolling out an in
2025-06-26 22:36'Call of Duty' figures out how to make loot boxes even more awful
2025-06-26 21:38Featured Posts
Bomb Envy
2025-06-26 23:22Tattooist creates mesmerising flipbook
2025-06-26 23:00Is TV on the internet still cheaper than cable?
2025-06-26 22:59Popular Articles
LG V30's camera will have some amazing specs
2025-06-26 23:29Is 'Sing Sing' streaming? How to watch the A24 drama at home.
2025-06-26 22:15Newsletter
Subscribe to our newsletter for the latest updates.
Comments (8756)
Warmth Information Network
Philips now allows customers to 3D print replacement parts
2025-06-27 00:04Creation Information Network
Elon Musk says story about fired assistant is 'total nonsense'
2025-06-26 23:29Co-creation Information Network
12 of the most beautiful office buildings in the world
2025-06-26 23:10Openness Information Network
Android O's name might be announced on the day of the solar eclipse
2025-06-26 22:37Evergreen Information Network
The 5 most inappropriate things Donald Trump said at a Puerto Rico disaster briefing
2025-06-26 22:03